Ever since one of my websites was hacked a few months ago, I have taken a much more personal interest in issues of cybersecurity. Whilst I have spoken and written many times on the subject, it is only when things really affect you in a personal way that you begin to gain different understandings of the issues. It represents a shift from a theoretical understanding to a practical one!
I thought I knew most of the various recommendations concerning password and PIN security, and that I had indeed followed them. However, no digital system is ever completely secure, and the level of sophistication now being used by those intent on stealing identity data, particularly with respect to banking information, is becoming very much more sophisticated.
There are many well known organisations providing advice and recommendations, such as Sophos, Symantec and Kaspersky Lab, but there are rather few places where all of this information is brought together in a single place. The level of insecurity, and the apparent disinterest among vast numbers of people in doing much about their digital security is not only surprising, but is also deeply concerning. So, in this posting, I have tried to bring together some of the more interesting observations that have recently been made about passwords and PIN numbers, in order to try to persuade people to take action on this really rather important topic!
Most popular PIN codes and iPhone passcodes
There are numerous articles on the most popular PIN codes – in other words the ones that no-one should actually use! One of the best is Daniel Amitay‘s experiment, where he used Big Brother’s passcode set up screen as a surrogate to estimate iPhone passcode usage, and discovered that the top ten codes listed below represented 15% of all passcodes used:
- 1234
- 0000
- 2580
- 1111
- 5555
- 5683
- 0852
- 2222
- 1212
- 1998
None of these are surprising, given that they represent easily remembered structures around the keypad. The passcode 1998 features because it is a year of birth and as Amitay goes on to point out other birth years also feature highly among passwords.
What is perhaps even more worrying is that research by Sophos in 2011 suggested that 67% of consumers do not even use any passcode on their ‘phones, so that a passer-by can access all of the information on the ‘phone without even having to bother to hack the code.
Four digit codes are also commonly used by banks to enable customers to access money through cashpoint machines (ATMs). Research summarised by Chris Taylor (on Mashable) notes that 27% of people use one of the top 20 PINs for their banking, with the most popular number (1234) being used by a massive 11%. The top 20 PIN codes he lists are as follows:
- 1234 (10.7%)
- 1111 (6.0%)
- 0000 (1.9%)
- 1212 (1.2%)
- 7777 (0.7%)
- 1004 (0.6%)
- 2000 (0.6%)
- 4444 (0.5%)
- 2222 (0.5%)
- 6969 (0.5%)
- 9999 (o.5%)
- 3333 (0.4%)
- 5555 (0.4%)
- 6666 (0.4%)
- 1122 (0.4%)
- 1313 (0.3%)
- 8888 (0.3%)
- 4321 (0.3%)
- 2001 (0.3%)
- 1010 (0.3%)
Chris Taylor goes on to comment that although there are 10,000 possible combinations of four digits, 50% of people use the most popular 426 codes! As he says, “Pick up an ATM card on the street, and you have a 1 in 5 chance of unlocking its cash by entering just five PINs. That’s the kind of Russian Roulette that’s going to be attractive to any casual thief”.
There is therefore really quite a high probability that even without watching someone enter their PIN number and then stealing the card, or using sophisticated technology to ‘crack’ someone’s PIN code, criminals would have a pretty good chance of accessing someone’s bank account just by using the most popular codes above. The implication for users is clear: use a PIN code that is not among the most common!
Passwords
The situation is scarcely better with passwords that people use for their online digital activities. Numerous surveys have all pointed to the same conclusion, that a very small number of passwords continue to be used by large numbers of people. These change a bit over time, and vary depending on cultural context and country, but the message is clear. Even without sophisticated programmes to crack passwords, those wishing to access personal information can achieve remarkable success just by trying to use the most common passwords! The most common passwords, in other words those to be avoided, are listed below:
|
Splashdata 2012
|
Sophos Naked Security 2010, based on leaked Gawker Media passwords
|
| 1 |
password
|
123456
|
| 2 |
123456
|
Password
|
| 3 |
12345678
|
12345678
|
| 4 |
abc123
|
lifehack
|
| 5 |
qwerty
|
qwerty
|
| 6 |
monkey
|
abc123
|
| 7 |
letmein
|
111111
|
| 8 |
dragon
|
monkey
|
| 9 |
111111
|
consumer
|
| 10 |
baseball
|
12345
|
| 11 |
iloveyou
|
0
|
| 12 |
trustno1
|
letmein
|
| 13 |
1234567
|
trustno1
|
| 14 |
sunshine
|
Dragon
|
| 15 |
master
|
1234567
|
| 16 |
123123
|
baseball
|
| 17 |
welcome
|
superman
|
| 18 |
shadow
|
iloveyou
|
| 19 |
ashley
|
gizmodo
|
| 20 |
football
|
sunshine
|
| 21 |
jesus
|
1234
|
| 22 |
michael
|
princess
|
| 23 |
ninja
|
starwars
|
| 24 |
mustang
|
whatever
|
| 25 |
password1
|
shadow
|
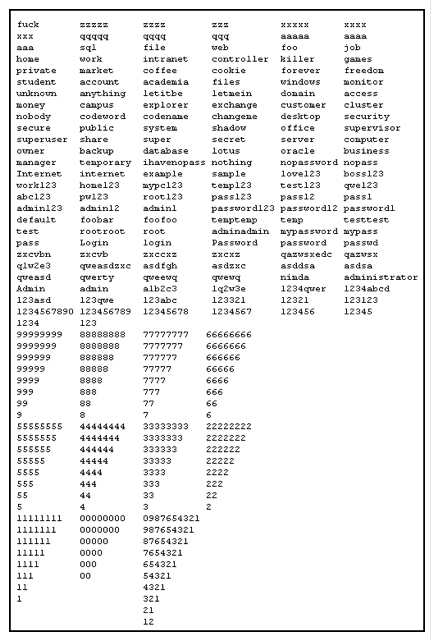
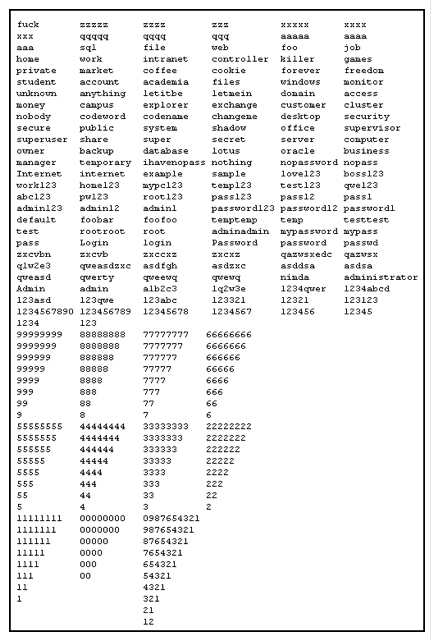
A slightly more sophisticated approach is that adopted by those wishing to break into networks by testing them automatically against a much larger number of different passwords. One of the best publicised accounts of this was the Conficker worm, which used the passwords in the chart below to try to access accounts (Sophos, 2009):
Again, this clearly indicates that considerable care needs to be taken in choosing passwords, and ensuring that they are at the very least more complex than those listed above.
Tips to reduce the risk of fraud through mobile devices and digital technologies
Much has been written about sensible advice for reducing the risk of fraud through mobile passcodes, banking PINs and online login passwords. Such tips will never eliminate really determined people from hacking into your identity, but a few simple steps can at least make it more difficult for the less determined. These include:
- Always secure your ‘phone with a PIN code, or better still a password (iPhone users can do this simply in Settings>General>Passcode Lock). This will help to prevent all of your contacts, photos, e-mails and other personal information being accessed immediately by anyone who picks up your ‘phone.
- Reduce the time before your ‘phone automatically locks so that it is as short as possible, preferably no more than a minute
- Always use complex passwords, that preferably include lower case and upper case letters, numbers and special characters
- Use passwords that are at least 8 characters and preferably more than 12 characters in length
- Frequently change your passwords at random intervals, so that possible hackers are unaware when to expect changes
- Use different passwords for different accounts, so that if one password is ‘broken’ this will not permit access to your other accounts
- Think about using a service that tests the strength of a proposed password (such as The Password Meter, Microsoft’s password checker, or Rumkin’s strength test) – for the hyper-security-conscious person, it is probably best to do this from a computer other than your own!
- Never, under any circumstances give your passwords or PIN codes to other people
Ultimately, passwords and PIN numbers are just part of a wider defence needed against digital theft. Human action, be it using the ‘phone in an unsafe public place or unfortunately responding to a phishing attack, is still the cause of much digital grief. As I write, Sophos has just for example reported a phishing attack through a security breach on the Ethiopian Red Cross Society’s website purporting to be a Google Docs login page.
If the worst happens, and you do lose a ‘phone there are at least two important things to do:
- Ensure you have software on the ‘phone that can enable you to track it (as with the Find My iPhone app, or for Android ‘phones there are apps such as Sophos’ Mobile Security app)
- If there is no chance of getting the ‘phone back, then remotely delete all of its content as swiftly as possible, remembering that if it has been backed up on a laptop or cloud facility, then all of the data can be restored at a later date.
Working together, and sharing good practices in personal digital security we can do much to help reduce digital identity theft.
 I am delighted to see Bill Dutton’s magisterial edited The Oxford Handbook of Internet Studies (Oxford University Press, 2013) just published. This is a really excellent and authoritative review of current research on all aspects of the Internet, with some 26 chapters from leading figures in the field. The 607 page book is divided into five main parts:
I am delighted to see Bill Dutton’s magisterial edited The Oxford Handbook of Internet Studies (Oxford University Press, 2013) just published. This is a really excellent and authoritative review of current research on all aspects of the Internet, with some 26 chapters from leading figures in the field. The 607 page book is divided into five main parts: